Unlocking Your Smart Home: Navigating the Complex World of Privacy and Security Risks

Smart home technology promises a future of unparalleled convenience, transforming everyday tasks with interconnected devices that can run your home, or even themselves. From voice-controlled assistants managing your lights and entertainment to smart thermostats optimizing energy use, and video doorbells enhancing security, these gadgets aim to make life easier and more seamless. However, this increasing interconnectedness comes with significant, often unseen, privacy and cybersecurity costs that every smart home owner needs to understand.
What Makes a Smart Home "Smart" and Why Does It Matter for Your Privacy?
The Internet of Things (IoT) connects our physical objects to the internet, allowing them to communicate with other devices and systems. Smart home devices are a subset of IoT specifically designed to optimize the home environment. Their "intelligence" relies heavily on continuously collecting, storing, and using vast amounts of user data from within your home and its surroundings. This includes:
- Voice recordings and transcripts from voice assistants, which learn your habits, preferences, and even infer personal traits like health information or financial status. They may even accidentally activate and record conversations not intended for the device.
- Movement patterns and occupancy data from smart thermostats via motion sensors, revealing when your house is empty, when specific rooms are used, and even sleeping patterns. If geofencing is enabled, they can track your location outside the home.
- Video and audio recordings from smart doorbells and security cameras, capturing visitors, unusual motion, and even enabling facial recognition.
- Identifying information like names, contact details, location data, payment information, and network credentials, collected during device setup.
- Data from connected third-party accounts, such as search history, calendar events, and even shopping lists.
Experts estimate that by 2025, IoT devices will generate almost 80 zettabytes of data annually, emphasizing the sheer volume of personal information at play.
The Alarming Privacy Concerns in Your Connected Home
The intuitive sense that our home is a private, protected space is challenged by smart devices, which expose our innermost lives to potential scrutiny. The reliance on immense amounts of data raises several critical privacy concerns:
- Invasive Inferences: Devices can draw surprisingly sensitive inferences about your life. For example, a voice assistant might infer pregnancy from search queries or daily routines from timestamps and device usage. Smart thermostats can reveal house layouts, movement patterns, and whether someone has trouble sleeping. Smart doorbells can infer a neighbor's routine or even a user's religion based on decorations.
- Improper Data Access and Use:
- Companies' Use: While data collection aids in device improvement and personalization, it's also used for invasive targeted advertising.
- Third-Party Sharing: User data can be shared with data brokers or other third parties, spreading personal information to entities users haven't consented to.
- Unauthorized Employee Access: Incidents like Ring employees having unrestricted access to video recordings, including those from "intimate spaces," highlight the risk of internal misuse.
- Government Surveillance: The continuous recording by numerous sensors, cameras, and microphones raises concerns about the potential for a future surveillance state.
- Lack of User Consent and Control: Many companies downplay privacy risks or claim they are "inescapable" for profit. Users often agree to data collection without fully reading lengthy consent forms. Furthermore, accidental activation of voice assistants can lead to unintended recordings of non-consenting individuals, including children and guests. Users also often lack the ability to completely delete collected data, effectively signing away their right to privacy.

Cybersecurity Vulnerabilities: When Your Smart Home Becomes a Target
Beyond privacy concerns, smart home devices present significant cybersecurity risks, making them attractive targets for hackers.
- Common Vulnerabilities:
- Outdated Firmware and Weak Default Passwords: Many devices are perpetually vulnerable due to unpatched software or easily guessable factory settings. This makes them "easy to hack".
- "Black Box" Devices: Many IoT devices are opaque, offering little visibility into their internal state, software, or external interactions, complicating security management.
- Inadequate Security Features: Some devices may not support strong credentials like multi-factor authentication or lack sufficient logging capabilities to detect incidents.
- Infamous Hacks and Real-World Impacts:
- Wi-Fi Router Compromise: Hacked routers can grant threat actors access to your entire network, enabling data theft, traffic monitoring, or redirection to malicious sites.
- Smart Thermostats: Hackers have famously accessed devices like Google Nest to control home temperatures and perform other malicious activities.
- Smart Speakers: Compromised smart speakers can be used to control other smart devices, access locked garages, or even place unauthorized online orders using stored credit card information.
- Baby Monitors and Security Cameras: These devices are particularly vulnerable if left on default passwords or with remote access enabled, leading to instances of unauthorized surveillance. Footage from unsecured cameras has been live-streamed online without homeowners' knowledge.
- Smart Appliances: Devices like smart refrigerators have been hacked, leading to the theft of credentials (e.g., Gmail credentials).
- Medical Devices: In 2017, a serious vulnerability was discovered in implantable pacemakers, illustrating the high stakes of security in medical IoT.
- Consequences of Neglecting Security: High-profile security lapses underscore the potential for disaster, including:
- Identity theft and fraud.
- Data theft over home or public networks.
- Unauthorized access and control of devices.
- Unwanted recordings of video or audio.
- Compromised physical safety.

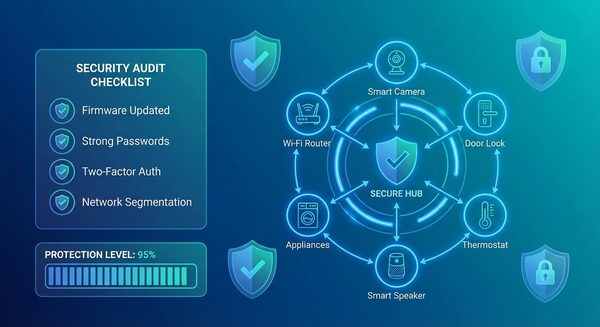
Protecting Your Digital Sanctuary: Essential Strategies and Solutions
Safeguarding your smart home requires a multi-faceted approach, combining proactive user actions with a demand for stronger security and privacy features from manufacturers.
What You Can Do (User Best Practices):
- Prioritize Strong, Unique Passwords and Multi-Factor Authentication (MFA): This is paramount for all smart devices and associated accounts. For critical devices like smart locks and security cameras, MFA is especially important. Consider using a password manager.
- Keep Software and Firmware Updated: Manufacturers frequently release updates that include security patches for known vulnerabilities. Always install these promptly.
- Segregate Your Network: Connect "headless" IoT devices (those without a display screen, like smart speakers or robotic vacuums) to a separate Wi-Fi network or SSID from your computers and cellphones. This limits potential access if one device is compromised.
- Review Privacy Policies and Settings: Understand what data your devices collect and how it's used. Actively seek and use privacy settings, and manage app permissions.
- Disable Unused Features and Remote Access: Reduce the attack surface by turning off features you don't use and disabling remote viewing when not needed.
- Be Vigilant Against Phishing: Phishing emails are a common tactic for hackers to gain login credentials.
- Consider Identity Theft and Cyber Protection Services: Enroll in services that can alert you to suspicious activity and provide resolution if identity fraud occurs.
What Manufacturers and Policymakers Should Do (Industry & Regulatory Responsibilities):
- Design Security and Privacy In: Security must be a foundational design principle, not an afterthought.
- Data Minimization: Devices should collect only the minimum amount of data necessary for their stated function.
- Pseudonymization: Use pseudonymization for personal data to make it harder to identify individuals even if data is stolen.
- Mandatory Encryption: Implement encryption for all data – whether in storage, in transit, or in use. End-to-end encryption should be used where possible.
- Secure Device Setup: Devices should come with unique, preprogrammed passwords and require users to set new, strong passwords upon initial setup.
- Automated Security Patches: Companies should automatically implement security patches and notify users, rather than relying solely on users to update devices.
- Robust Access Control: Implement strong access controls to prevent internal data misuse or breaches.
- Federated Learning: Utilize privacy-preserving machine learning techniques like federated learning, which train models on local data without transferring raw user data to external servers.
- Offer Local Storage/Processing Options: Provide users with the choice between local and cloud storage/processing, especially for sensitive data.
- Enhance Transparency and Understandability: Companies should clearly and understandably inform users about data operations, privacy policies, and how they handle security threats.
- Flexible Privacy Settings: Make features that raise privacy concerns (e.g., sharing data with neighbors) opt-in, not default. Allow users to easily delete their data upon device abandonment.
- Unified Device Data Format: Implementing a unified device data format protocol across different brands could significantly improve personal information protection and user choice, as products could communicate without proprietary constraints.
- Consensus Mechanisms: Integrate technologies like the Byzantine general problem method to confirm whether a device is controlled by its legitimate owner, enhancing overall security.

The Path Forward: Building Trust in the Connected Home
Consumer trust is a key differentiator in the smart home market. The industry must recognize that many consumers are concerned about data security and privacy, and these concerns act as significant barriers to wider adoption.
Educating customers about risks and available protective measures, and designing products with transparent and robust privacy and security features, will not only prevent harm but also foster greater confidence and drive market growth. The goal is to ensure that the undeniable benefits of a connected home do not come at the expense of our personal privacy and digital well-being.