The Summer of Smart Scrutiny: A 2025 Retrospective on IoT Security and Privacy

For the world of the Internet of Things (IoT), the summer of 2025 will be remembered not for its groundbreaking new gadgets, but for the harsh light it shone on the persistent security and privacy failures within them. It was a season that brought a stark realization to the forefront: the convenience of a connected life comes with a hidden cost, and threat actors are becoming increasingly adept at exploiting it.
From massive botnets hijacking our streaming devices to sophisticated new attacks that can turn AI against us, this summer was a critical turning point. For every new smart refrigerator that can suggest a recipe, a new risk to our personal data has emerged. This is the essential rundown of the smart home security and privacy landscape from the summer of 2025.
The Trojan in the Living Room: The Rise of the BADBOX 2.0 Botnet
The most significant threat to smart homes this summer was the emergence and explosion of the BADBOX 2.0 botnet. The FBI issued a stark warning in June, revealing that millions of IoT devices, primarily low-cost, uncertified Android-based products, were being shipped with malware pre-installed or were infected during the initial setup process.
What You Gotta Know:
- The Targets: The campaign has been found on a wide range of devices, including generic TV streaming boxes, digital projectors, and even some aftermarket vehicle infotainment systems, most of which are manufactured in China.
- How it Works: The malware, often hidden within required setup applications from unofficial marketplaces, creates a backdoor into the user's home network. Once connected, these infected devices become part of a massive botnet that can be used for a variety of criminal activities, including:
- Residential Proxy Services: The botnet sells access to your home's internet connection, allowing other cybercriminals to route their malicious traffic through your network, effectively hiding their own location and making it appear as though the attacks are coming from you.
- Large-Scale Attacks: These compromised devices can also be used to launch Distributed Denial-of-Service (DDoS) attacks or to mine for cryptocurrency, all while consuming your bandwidth and electricity.
- The Scale of the Problem: The FBI has stated that the BADBOX 2.0 botnet consists of millions of infected devices, creating a global network of compromised home networks that can be exploited for a wide range of criminal activities.
The Unseen Threat: "OneFlip" and the Hacking of AI
While botnets are a familiar threat, this summer saw the emergence of a new, more insidious type of attack that targets the very intelligence of our smart devices. Researchers unveiled "OneFlip," a Rowhammer-based attack that can flip a single bit in the weights of a neural network.
What does this mean in plain English?
Imagine the "brain" of an AI system is made up of millions of tiny switches. A OneFlip attack allows a hacker to flip just one of these switches, subtly but critically altering the AI's behavior. The most alarming aspect is that this can be done without degrading the AI's overall performance, making it nearly impossible to detect.
Potential Consequences for Smart Homes:
- Facial Recognition Failure: An attacker could use a OneFlip attack to create a "backdoor" in a smart security camera, causing it to fail to recognize an intruder's face or, even worse, to recognize an intruder as a trusted family member.
- Autonomous Vehicle Mayhem: While not strictly a "smart home" device, the same principle applies to other AI-driven technologies. A OneFlip attack could cause a self-driving car to misinterpret a stop sign or to fail to recognize a pedestrian.
This attack represents a new frontier in AI security, moving beyond simple data breaches to the manipulation of the very logic that powers our smart devices.
Privacy Under Scrutiny: New Regulations and the "Right to Be Forgotten"
It wasn't all bad news this summer. On the regulatory front, there has been a significant push to hold manufacturers accountable for the security and privacy of their products.
- The EU's Cyber Resilience Act (CRA): This new regulation, now in effect, mandates that any product with digital elements sold in the EU must meet strict cybersecurity requirements throughout its lifecycle. This includes conducting security audits, providing regular security updates, and being transparent about vulnerability handling.
- The U.S. Cyber Trust Mark: While facing some recent delays due to an FCC investigation, the U.S. is moving forward with its own "Cyber Trust Mark" program. This will be a voluntary labeling program, similar to the Energy Star symbol, to help consumers identify IoT products that meet federal cybersecurity standards.
However, a major privacy challenge remains unresolved: the "Right to be Forgotten" in the age of AI. While you can request that a company delete your data, it's currently almost impossible for them to remove your data from a trained AI model. This means that even after you've deleted your account, your information may still be part of the underlying knowledge of the AI systems that power our smart assistants and other devices.
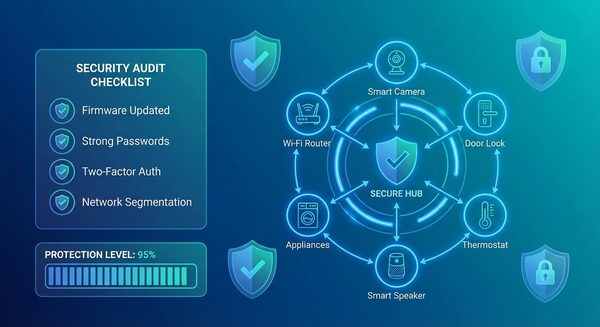
What You Can Do: A Summer 2025 Security Checklist
The events of this summer have made it clear that we can't simply trust that our smart devices are secure out of the box. Here are the essential steps every smart home owner should take now:
✅ Avoid Uncertified, Off-Brand Devices: The BADBOX 2.0 botnet is a powerful reminder that "too good to be true" deals on generic smart devices often come with a hidden security cost. Stick to reputable brands that have a clear commitment to security and regular updates.
✅ Change Default Passwords Immediately: This is the single most important step you can take. Never use the default password that comes with a device.
✅ Segment Your Network: Create a separate "guest" Wi-Fi network for all of your IoT devices. This will prevent a compromised smart light bulb from being able to access your laptop or other more sensitive devices.
✅ Regularly Audit and Update: Check for firmware updates for all of your smart devices at least once a month. If a manufacturer is not providing regular updates, that is a major red flag.
✅ Be Mindful of Data Collection: Before you buy a new smart device, read its privacy policy. Understand what data it collects, where it's stored, and how it's used. If you're not comfortable with the policy, don't buy the device.
The Summer of Smart Scrutiny has shown us that the future of the smart home is a double-edged sword. The same technologies that bring us convenience and automation also open the door to new and sophisticated threats. By staying informed and taking a proactive approach to security, we can enjoy the benefits of a connected life without sacrificing our privacy and safety.