The Complete Guide to Securing Your Smart Home Network in 2026: From Setup to Fort Knox
Executive Summary
Your home Wi-Fi network is the foundation of your smart home's security — and the weakest link cybercriminals target first. With 71% of IoT devices connecting via Wi-Fi and home networks experiencing an average of 29 attack attempts daily, securing your network is no longer optional. This comprehensive guide walks you through building an impenetrable network fortress, from basic WPA3 encryption to advanced segmentation strategies, VPN deployment, and intrusion detection. Whether you're setting up your first smart device or managing 20+ connected gadgets, this step-by-step blueprint will transform your vulnerable home network into a security stronghold.
Why Your Network Is the #1 Target
Before diving into solutions, understand why attackers focus on home networks:
The Network Is the Gateway
Once a hacker breaches your Wi-Fi, they gain access to:
- Every connected device (cameras, locks, thermostats, computers, phones)
- All network traffic (passwords, credit cards, private messages)
- Your internet connection (to launch attacks against others)
- Physical security controls (smart locks granting home entry)
Home Networks Are Easy Targets
Most home networks have:
- Weak passwords (short, dictionary words, family names)
- Outdated encryption (WEP, WPA, weak WPA2)
- Default router settings (unchanged admin passwords)
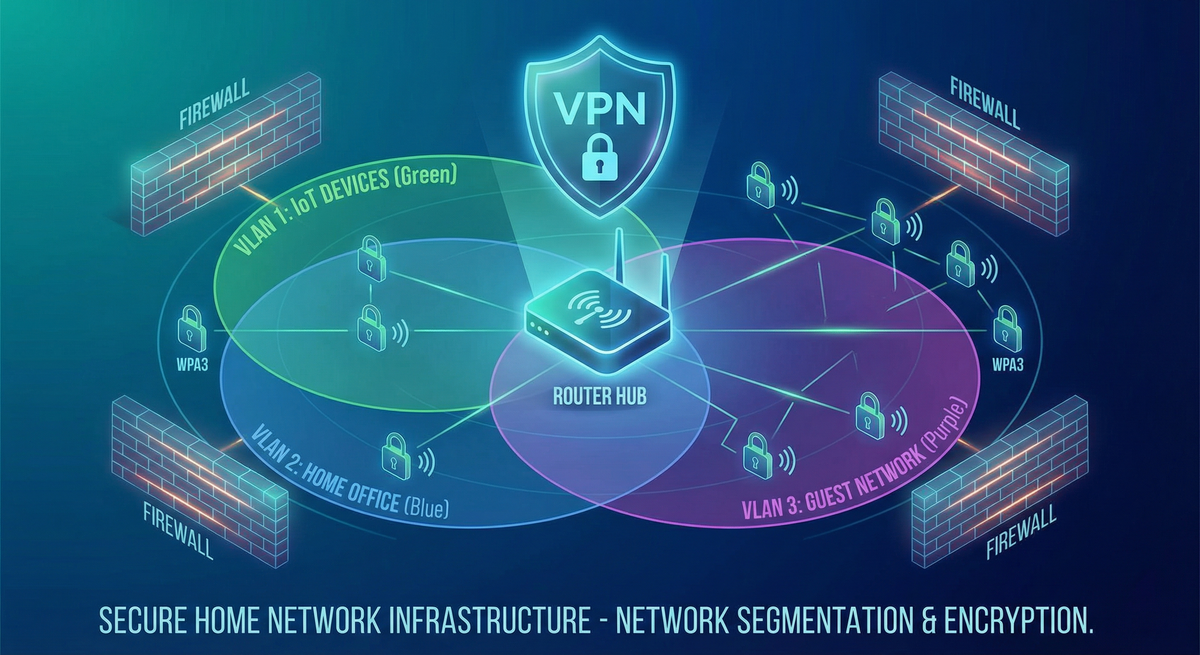
- No segmentation (all devices on one network)
- Disabled firewalls (for convenience or gaming)
- No monitoring (users never check logs)
The Statistics Paint a Grim Picture
2026 Home Network Threat Data:
- 29 attack attempts per household daily
- 46% of employees connect personal IoT to work networks
- 52% of organizations experienced attacks via IoT devices
- 71% of IoT devices use Wi-Fi (creating massive attack surface)
- Average time to breach weak Wi-Fi: 2-10 hours
Real-World Attack Scenario
Hour 0: Attacker parks outside your home with laptop
Hour 1: Scans for Wi-Fi signals, identifies your network
Hour 2-8: Automated password cracking tools work
Hour 9: Access gained to your network
Hour 10: Device reconnaissance begins (identifying cameras, locks, computers)
Hour 12: First device compromised (often a camera or router)
Hour 24: Full network control, data exfiltration begins
Week 1: Months of surveillance without detection
This isn't theoretical. It happens thousands of times daily.
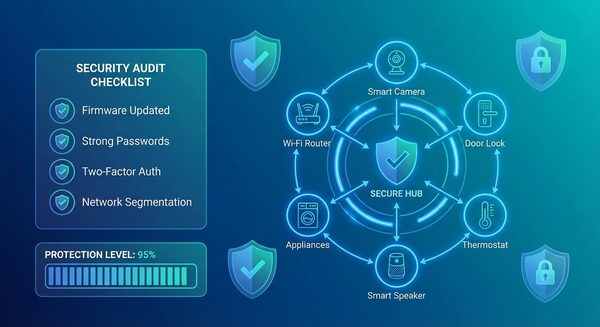
The 5-Layer Network Security Framework
Building a secure smart home network requires five integrated layers. Each layer adds defense depth, ensuring multiple barriers between attackers and your devices.
Layer 1: Router Security Hardening
Your router is the gatekeeper. If it's compromised, nothing else matters.
Step 1: Change the Default Admin Password
Why It Matters:
Routers ship with default admin credentials that are publicly documented online. Hackers maintain databases of default passwords for every router model. If you haven't changed yours, you're vulnerable.
How to Change It:
- Access router admin panel (usually
192.168.1.1or192.168.0.1) - Log in with current credentials (check router label or manual)
- Navigate to Administration → Password
- Create a 16+ character password with mixed characters
- Save and log back in to verify
Password Requirements:
- Minimum 16 characters
- Mix of uppercase, lowercase, numbers, symbols
- No dictionary words
- Unique to this router (not used elsewhere)
Example Strong Password:
Tr0ut&Maple$2026!Network
Step 2: Disable WPS (Wi-Fi Protected Setup)
Why WPS Is Dangerous:
WPS allows devices to connect via push-button or 8-digit PIN. The PIN method has a critical vulnerability: attackers can brute-force it in 4-10 hours.
How to Disable:
- Router admin panel → Wireless Settings → WPS
- Toggle OFF or Disable
- Save settings
Alternative: If you need easy connection, use WPS for setup only, then immediately disable it.
Step 3: Update Router Firmware
Why Firmware Matters:
Router vulnerabilities are discovered constantly. Outdated firmware contains known exploits that hackers actively target.
How to Update:
Automatic Updates (Best):
- Router admin panel → Administration → Firmware
- Enable "Automatic Updates"
- Set update schedule (e.g., 3 AM weekly)
Manual Updates:
- Visit manufacturer website
- Download latest firmware for your exact model
- Router admin panel → Administration → Firmware Update
- Upload file and install
- Router will reboot (5-10 minutes)
Update Frequency:
- Check monthly minimum
- Enable notifications for critical security patches
Step 4: Enable the Router Firewall
Why Firewalls Matter:
Firewalls block unauthorized incoming connections and can filter malicious traffic patterns.
How to Enable:
- Router admin panel → Firewall or Security
- Enable "SPI Firewall" (Stateful Packet Inspection)
- Enable "DoS Protection" (Denial of Service)
- Enable "Block Ping from WAN" (prevents reconnaissance)
- Save settings
Additional Firewall Features:
- Port forwarding rules: Only open ports you specifically need
- DMZ: Never use DMZ for smart home devices
- UPnP: Disable unless specific apps require it (creates security holes)
Step 5: Disable Remote Management
Why Disable It:
Remote management allows router configuration from the internet. Unless you have a specific need, this creates an unnecessary attack vector.
How to Disable:
- Router admin panel → Administration → Remote Management
- Set to "Disabled" or "Off"
- If needed, restrict to specific IP addresses only
- Save settings
Step 6: Change the Default Router IP Address
Why Change It:
Default router IPs (192.168.1.1, 192.168.0.1) make it easier for malware to find and attack your router.
How to Change:
- Router admin panel → LAN Settings → Router IP
- Change to uncommon address (e.g.,
10.22.44.1) - Save (router will reboot)
- Access router using new IP going forward
Note: This breaks bookmarks, so update them.
Layer 2: Wi-Fi Encryption & Authentication
Encryption protects data traveling between devices and your router.
Step 1: Upgrade to WPA3 Encryption
Why WPA3:
WPA3 is the latest Wi-Fi security standard, offering:
- 192-bit encryption (vs. 128-bit in WPA2)
- Protection against brute-force attacks
- Forward secrecy (past traffic stays encrypted even if password compromised)
- Protection on public networks (individualized data encryption)