Secure IoT House 2026: The Complete Guide to Smart Home Security & Privacy
Your home should be your sanctuary—a safe haven from the outside world. But as homes become "smarter," they're also becoming more vulnerable. By 2026, the average American household contains 22 connected devices, from smart speakers and thermostats to security cameras and even refrigerators. Each represents convenience and efficiency, but also a potential entry point for cybercriminals.
This comprehensive guide provides everything you need to know about securing your smart home in 2026, protecting both your privacy and your family's safety in an increasingly connected world.
The Smart Home Revolution: Numbers That Demand Attention
The smart home market has reached critical mass. In 2025, 69.91 million U.S. households actively use smart home devices, with the market expected to hit $250.6 billion by 2029. Globally, an estimated 41.6 billion IoT devices are now in use, generating nearly 79 zettabytes of data annually.
But this explosive growth comes with serious consequences:
- 13.6 billion attacks detected on consumer IoT devices between January and October 2025
- Nearly 30 attack attempts per day on the average connected home (triple the rate from 2024)
- 12 million threats blocked daily by security technologies across smart homes worldwide
- One in three data breaches now involves an IoT device
- 80% of IoT devices remain vulnerable to a wide range of attacks
Perhaps most concerning: even in 2025, an estimated 20% of IoT devices are still protected only by default login credentials that any attacker can find with a simple web search.
Understanding the Threat Landscape
Real-World Attack Examples
The dangers aren't theoretical. They're happening right now:
The Mirai Botnet Legacy: In 2016, the Mirai botnet hijacked hundreds of thousands of ordinary IoT devices—home routers, security cameras, DVRs—and weaponized them to launch record-breaking distributed denial-of-service attacks exceeding 1 terabit per second, knocking critical internet services offline.
Baby Monitor Hacks: Parents worldwide have experienced harrowing invasions when hackers took control of baby monitors and Wi-Fi security cameras. Some families heard strangers' voices speaking to their children through compromised devices. In one lawsuit, dozens of people reported receiving death threats and vile abuse after their in-home cameras were breached.
Smart Lock Compromises: Attackers have exploited vulnerabilities in smart locks to gain physical access to homes, with compromised devices leading to break-ins in residences and hotels.
Data Exposure Incidents: Recent breaches exposed billions of records containing Wi-Fi credentials, device IDs, and household geolocation data—providing attackers with comprehensive blueprints of home networks and routines.
The 2026 Threat Categories
Smart home attacks typically fall into two main categories, each with real consequences:
1. Network and Access Attacks (70% of threats)
- Unauthorized network access attempts
- Credential stuffing using leaked passwords
- Man-in-the-middle attacks intercepting communications
- Exploitation of unpatched firmware vulnerabilities
- Lateral movement from compromised devices to other network systems
2. Privacy and Surveillance Threats (30% of threats)
- Unauthorized access to cameras and microphones
- Collection of behavioral and routine data
- Location tracking and geofencing exploitation
- Smart speaker conversation harvesting
- Third-party data sharing without consent
Most Vulnerable Device Categories
Research shows specific device types face disproportionate risk:
- Streaming Devices & Smart TVs (30%): Entertainment equipment accounts for nearly one-third of all vulnerabilities
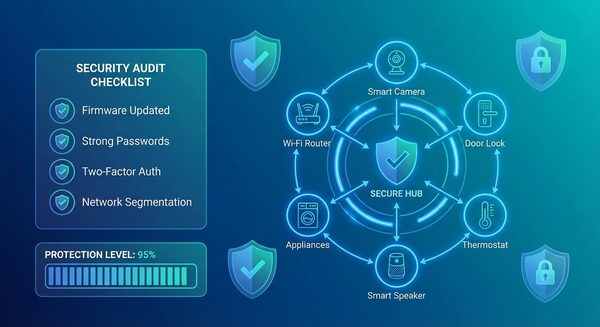
- IP Cameras (9%): Intended for safety but frequently compromised due to weak security and infrequent updates
- Smart Speakers (8%): Voice assistants like Alexa collect up to 28 out of 32 possible data points
- Smart Locks (7%): Direct physical security implications
- Smart Thermostats (6%): Can reveal occupancy patterns and schedules
- Wi-Fi Routers: The gateway to everything—when compromised, all connected devices are at risk